A Modern Framework for Fraud Prevention in Middle East Banking
A Modern Framework for Fraud Prevention in Middle East Banking
A Modern Framework for Fraud Prevention in Middle East Banking
Rapid digital adoption is reshaping banking across the Middle East. Instant onboarding, digital wallets, and super apps are now the norm, expanding the attack.
Author
Team Bureau



See how Bureau has helped industry leaders defend against networked Industrial-scale frauds →
Schedule a Demo
TABLE OF CONTENTS
See Less
The Middle East has always been a front runner amongst most of its regional counterparts.
Across Saudi Arabia, the United Arab Emirates, and the wider GCC (Gulf Cooperation Council), digital banking is now a lifestyle that citizens have embraced with ease.
In the UAE alone, at least 89% of consumers now use digital-first bank accounts. Cash, as a payment method, is slowly receding as digital payments grow in volume.
This rapid digital adoption is forcing banks to offer faster and smoother customer experiences. Instant account opening, digital wallets, app-based loans and super apps for personal finances have become a new banking culture in the Middle East. But, this speed comes at the cost of opening up new vulnerabilities for attackers.
When banking and financial institutions prioritize velocity and frictionless CX over security, connected intelligence takes a hit. Without connected intelligence: that includes linking identity, device, and behavior signals, banks and account holders are exposing themselves to serious fraud risks.

The rise of AI-driven and social engineering aided fraud
Digital fraud is largely driven by AI and social engineering. Instead of stolen credentials, criminals are now deploying AI-generated voices and deepfake media that impersonate innocent account holders and decision-makers.
Unlike traditional fraud practices, AI-enabled tactics have a strong layer of credibility, which makes them even more dangerous and convincing to a layman user.
They usually take the form of:
Voice cloning: Scammers recreate the voices of decision-makers through publicly available audio. Using these spurious voices, they call up family members or sub-ordinates to make wire transfers or urgent payments.
AI-generated video: Using deepfake videos, fraudsters simulate the actions and mannerisms of actual users. Video snippets feature financial distress or payment requests that are channeled to fraudster-controlled accounts for siphoning off money.
Automated script creation: Fraudsters use AI to generate personalized scam messages at scale, targeting users who respond assuming they are original messages. For example, fake penalty intimation messages from government agencies with a link that redirects to a fake payment link.
Related Read: Social Engineering Tactics: Exploring the ‘Human’ Angle in Fraud
When OTPs and basic KYC are no longer strong defenses
Most banks send one-time passwords (OTPs) as multi-factor authentication checks (MFA) to prevent fraud. However, these controls are no longer strong defenses against users being manipulated into executing fraudulent transactions.
OTPs are futile against AI-based voice and text messages that mimic a real user.
Basic KYC checks focus more on verifying credibility of the documents rather than establishing the context or intent of the interaction.
Personal information scraped from online sources is sufficient to run scams that seem authentic, as if they are being used by the user themselves.
But, not all hope is lost. Banks are raising their defenses using behavioral and device intelligence. This threat insight helps differentiate normal users from fraudsters and stop a fraudulent transaction early in its tracks.
Related Read: Understanding Device Intelligence: How It Works and Its Importance in Fraud Prevention
Some of these risk signals include:
Behavior patterns: Unique personal traits of the user like typing speed, navigation paths, and interaction duration that vary from past patterns.
Device risk: Unusual device configurations, emulators, or varying device metadata at onboarding or login stage.
Network context: Access from unfamiliar IP ranges or via anonymization services like VPN that may indicate bot activity.
Risk-based authentication vs forced verification
Fraud and customer experience occupy two extreme sides of a scale. Authentication is placed right at the center of these two. Frictionless CX can increase fraud risk, while adding more checks can disrupt customer experience. However, despite the positive intent, additional verification may not prevent fraud and might even introduce more vulnerabilities.
Related Read: Risk-Based Authentication: How Can It Help Your Business?
At a high level, digital banks rely on two different approaches: forced verification and risk-based authentication. The difference between them can directly impact fraud losses, customer trust, and conversion rates.
Risk-based authentication | Forced authentication |
|---|---|
Evaluates risk in real time using context, behavior, and device signals | Applies the same verification steps to all users and sessions |
Only when risk increases or signals change | Every login, transaction, or rule-based event |
Low friction for trusted users | High friction for all users |
Improves onboarding and login completion | Increases drop-offs and abandonment |
Recognizes known users on known devices | Re-verifies users repeatedly |
How trusted device binding helps reduce unnecessary challenges
In the face of fraud and customer experience trade-off, the most effective friction-reduction strategy is trusted device binding.
When a bank can reliably recognize a customer’s device, it establishes a certain amount of trust that can be carried off across multiple sessions.
This allows the bank to:
Skip redundant challenges for identified devices.
Detect risky changes, such as device resets or use of emulators.
Flag account access from new or manipulated devices.
In short, device trust does not replace identity checks. It complements them by answering a different question: Is this interaction happening from a device or environment that is trustworthy?
Country and regulatory landscape
Fraud is border-agnostic. It doesn’t stop at GCC borders, nor does it restrict itself to one specific digital banking channel.
This universal applicability of fraud is forcing regulators to tighten controls around monitoring, traceability, and accountability. Especially in the GCC countries, the result is a regulatory landscape that is locally distinct, yet increasingly aligned in outcomes.
Here is a brief overview of the regulatory landscape at the two most prominent GCC countries: Saudi Arabia and UAE.
Saudi Arabia (SAMA): Transaction integrity at scale
Saudi Arabia has one of the fastest-growing digital payment ecosystems in the region. According to Saudi Central Bank (SAMA), in 2024, e-payments accounted for 79% of all retail payments. Instant payments, wallets, and rapid fintech growth are the key drivers behind this digital payment adoption.
SAMA’s regulatory framework is also fine-tuned to tackle this scale of transactions:
Real-time transaction monitoring across payments and transfers.
Strong Anti-Money Laundering (AML) and CTF (Counter-Terrorism Financing) alignment, especially for instant payments and remittances.
Growing emphasis on behavioral consistency and anomaly detection, not just static rules.
As transaction volume and velocity continue to increase, SAMA’s regulations are shifting from reactive controls to continuous monitoring. Banks are expected to explain what the decision was, as also why it was made and whether any earlier risk signals were ignored.
Related Read: Decoding KSA's SAMA Mandate
UAE: Digital identity, KYB, and open finance
The UAE’s regulatory approach is strongly leaning towards digital trust and ecosystem participation.
It is indicated by key developments such as:
National digital identity frameworks enabling remote onboarding and authentication.
Stricter KYB requirements for platforms, marketplaces, and payment intermediaries.
Expansion of open finance, increasing data sharing across regulated entities.
Cross-border fraud: A shared regional risk
It is evident that remittances and cross-border payments are a core part of the GCC economy. The region processes at least 30 billion dollars annually in outbound and inbound remittance flows, with Saudi Arabia and the UAE ranking among the world’s top remittance corridors.
This creates shared fraud challenges across the region, primary risks being:
Account and mule reuse across countries.
Scams initiated in one jurisdiction and executed in another.
Limited visibility when fraud signals sit in separate national systems.
Fraud patterns do not care for regulatory borders, but risk systems do. It is here that connected intelligence matters the most.
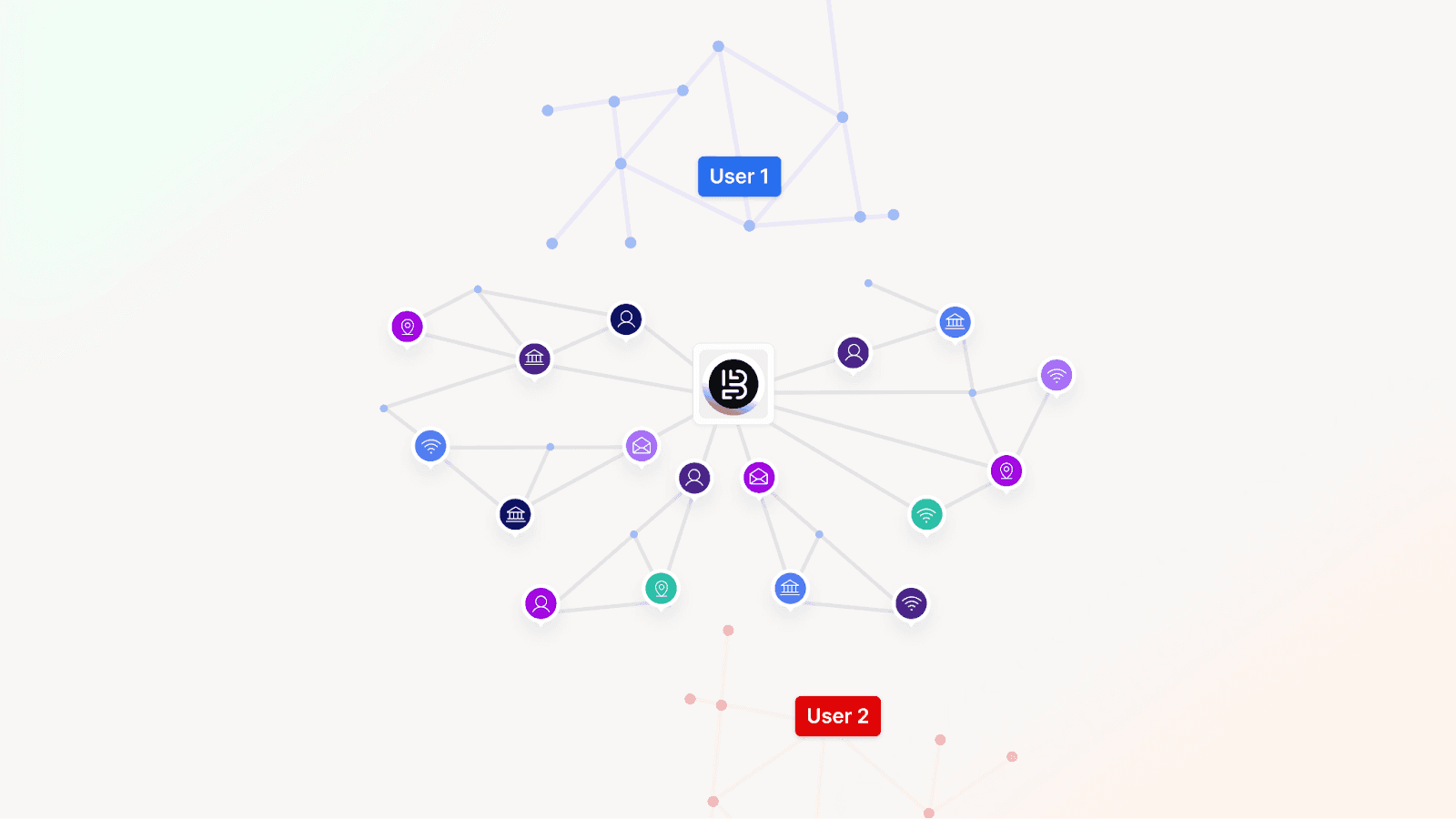
Why connected intelligence matters at regional scale
As GCC regulators raise expectations, the existing fragmented controls create blind spots. Connected intelligence can solve for this by linking:
Identity - Who the user is claiming to be.
Device - Which device they are using from and through which service.
Behavior - Individual actions and interactions over a period of time.
This connected intelligence helps detect fraud earlier, stop it from spreading across the region, and ultimately provide regulators with clear, auditable decision trails.
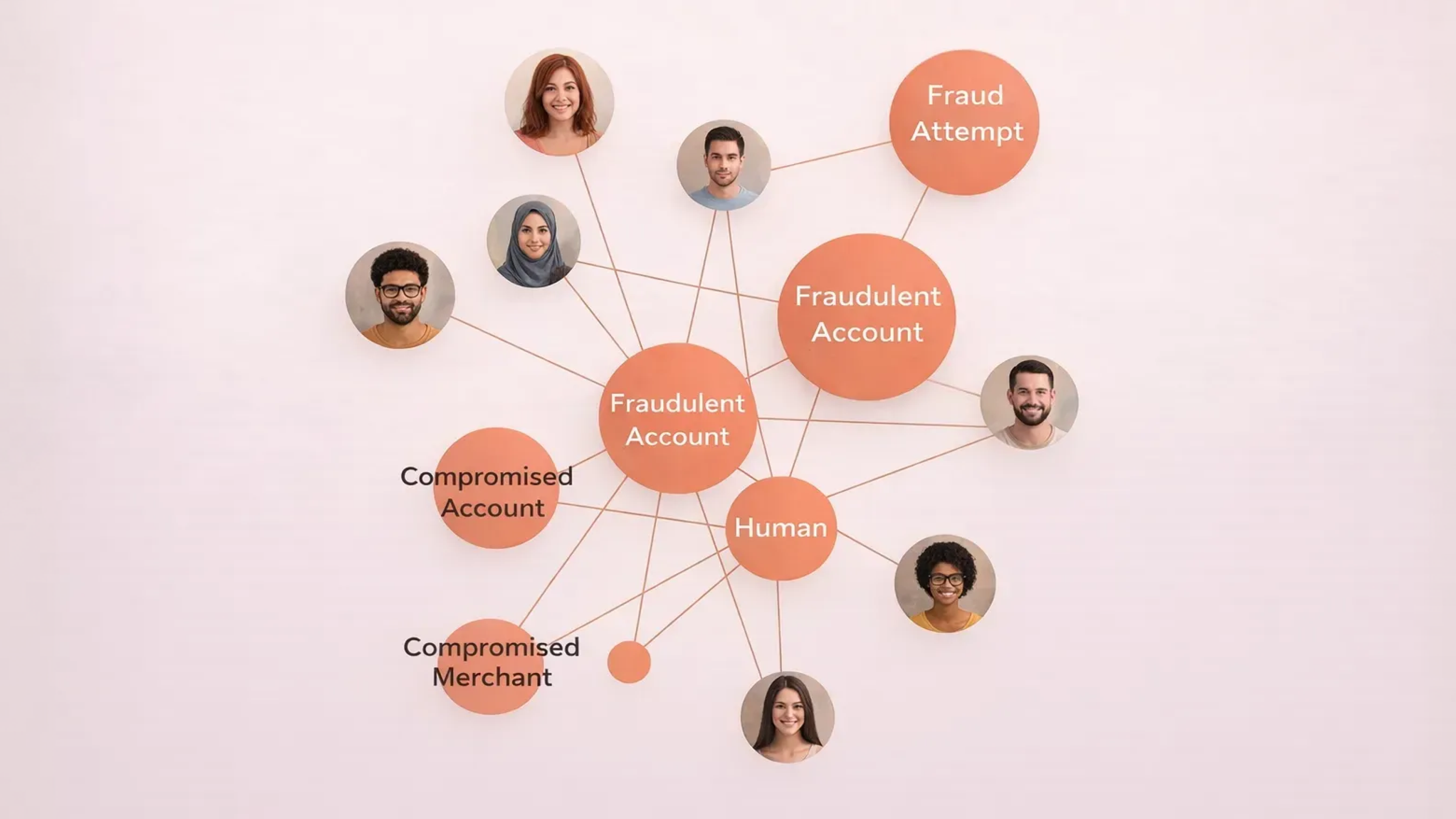
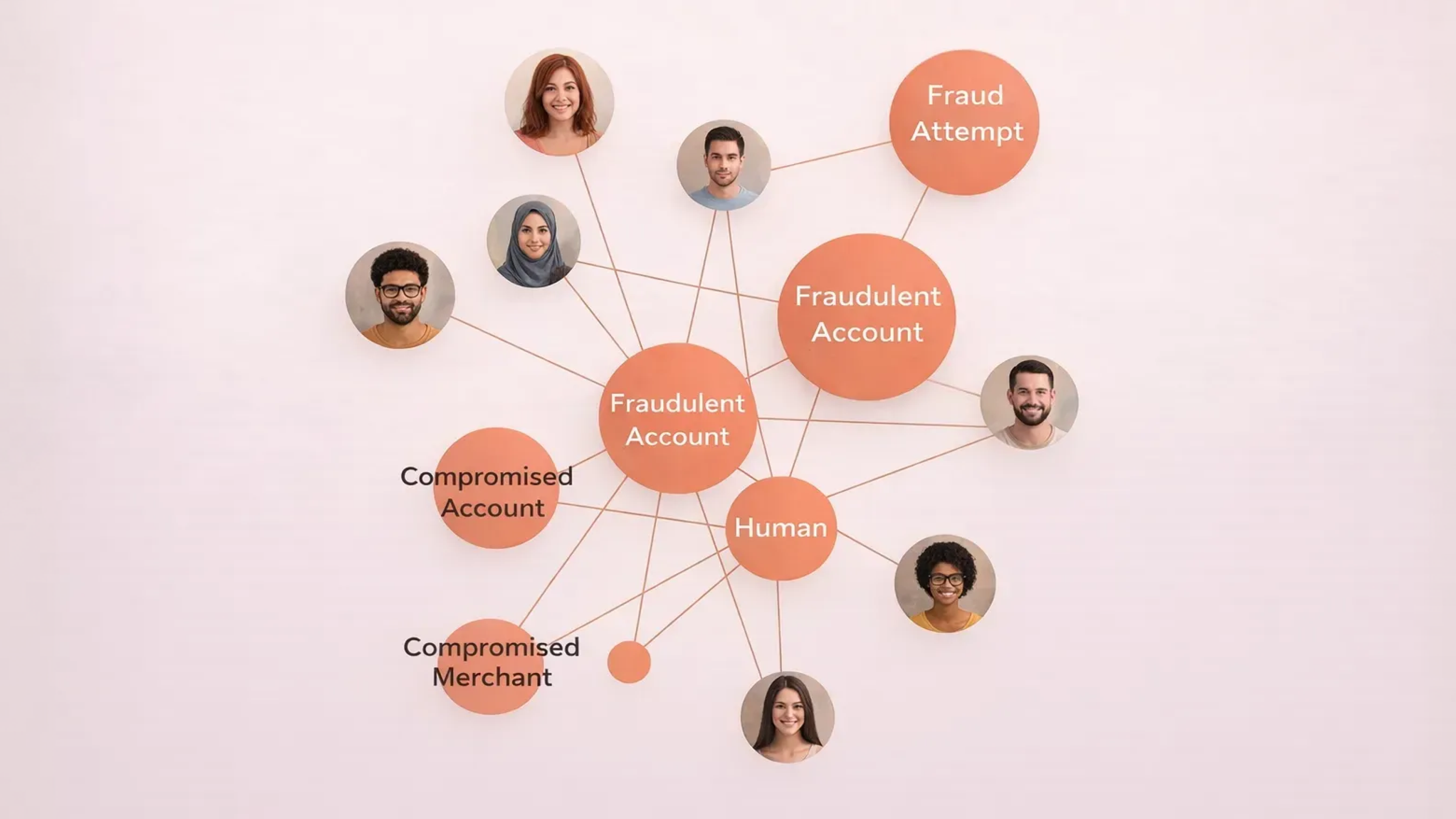
Why documents alone no longer establish trust
Document checks are essential for onboarding, but they were designed for a different threat model that was applicable at a different time period. The primary purpose of documentation is to confirm whether a document is real and pertains to the user who is applying for the service. They, however, have little control over how an account is used after approval, or whether the same identity is used by multiple accounts, devices, or sessions.
As fraud shifts toward fake identities and mule activity, one-time verification is an inadequate form of security.
Also, attackers have become adept at bypassing document-led controls using emulator farms, virtual cameras, and rooted or jailbroken devices. These environments can simulate the clean onboarding signals that fraud systems look for, while hiding automation and coordination of the bigger fraud network.
Once these accounts are active, the same devices and behavioral patterns often reappear across logins, payments, and transfers. Document checks fail to flag off these links because they operate in isolation and have limited relevance after onboarding.
Modern fraud prevention requires advanced techniques like device fingerprinting and graph-based detection to uncover these hidden connections.
Device and behavior signals persist across time, products, and identities, allowing banks to identify shared infrastructure used to run a network of synthetic accounts and mule networks.
Related Read: A Food Delivery Company Eliminates a 2,700+ User Fraud Ring
This shifts trust from a single one-point checkpoint to a living, breathing risk signal.
Bureau believes one-time verification is inadequate to establish trust. It needs to be continuously observed, correlated, and re-evaluated as users interact with the system.
Rethinking build vs buy in Middle East fraud systems
As fraud risk grows more complex, banks in the Middle East are confronted with a binary choice. They can either choose to build large parts of their fraud stack in-house, or rely entirely on off-the-shelf platforms.
In practice, neither extreme works well. Building everything from ground-up internally slows down time-to-value and puts a heavy burden on engineering teams. Buying rigid systems restricts control and adaptability. Banking leaders have a third option: which is buying the foundation and building differentiation on top. This hybrid approach balances speed, compliance, and long-term flexibility without piling up technical debt or stretching resources.
Related Read: From In-House Tools to Unified Fraud Intelligence
Why a hybrid approach is the best bet for the Middle East
As discussed earlier, banks in the GCC operate under fast-moving regulatory expectations and high transaction volumes. Therefore, maintaining in-house device intelligence and fine-tuning it to stay abreast with evolving fraud tactics and compliance requirements can be a big ask. The build-on-top model helps ease the situation by supporting real-time risk decisioning based on variables like products, region, and customer preferences.
Dimension | Build in-house | Buy off-the-shelf | Buy the foundation, Build differentiation |
|---|---|---|---|
Time-to-value | Usually slow, taking anywhere from months or years | Fast initial rollout | Fast foundation with incremental gains |
Engineering effort | High ongoing cost for maintenance | Low upfront effort | Focused on value, not plumbing |
Fraud coverage | Narrow at launch, expands slowly | Broad but generic | Broad foundation with tailored controls |
Device & behavioral intelligence | Complex to build and maintain | Often opaque or limited | Provided as a core layer, extensible |
Compliance readiness | Heavy internal burden | Depends on vendor transparency | Shared responsibility with clear auditability |
Adaptability to new fraud | High, but resource-intensive | Limited by vendor roadmap | High, with internal control |
Operational drag | Increases over time | Hidden constraints emerge | Kept low by design |
Regional scalability | Difficult to replicate across geos | One-size-fits-all | Designed for multi-country use |
Fraud prevention in 2026 in the Middle East
In 2026 and beyond, fraud prevention in the Middle East will be defined by the continuity of transactions and not static checks. Risk decisions will not be restricted to standalone junctures like onboarding or payment approval. Banks will have always-on risk monitoring that pan the full customer lifecycle.
Related Read: Onboarding Trusted Users at Scale with Bureau
However, this shift calls for a major upgrade in risk decisioning. Siloed tools will have to make way for connected intelligence that can connect the dots and explain risk clearly. The goal is not to have more alerts or controls, but to unearth blind spots faster and make decisions confidently.
Fraud prevention will no longer be restricted to a collection of tools. It will evolve into a connected system that observes trust continuously, adapts to change, and scales across products, users, and even borders.
Move from isolated controls to connected risk intelligence.See how Bureau provides always-on monitoring and improves fraud detection across onboarding, login, and transactions. |
The Middle East has always been a front runner amongst most of its regional counterparts.
Across Saudi Arabia, the United Arab Emirates, and the wider GCC (Gulf Cooperation Council), digital banking is now a lifestyle that citizens have embraced with ease.
In the UAE alone, at least 89% of consumers now use digital-first bank accounts. Cash, as a payment method, is slowly receding as digital payments grow in volume.
This rapid digital adoption is forcing banks to offer faster and smoother customer experiences. Instant account opening, digital wallets, app-based loans and super apps for personal finances have become a new banking culture in the Middle East. But, this speed comes at the cost of opening up new vulnerabilities for attackers.
When banking and financial institutions prioritize velocity and frictionless CX over security, connected intelligence takes a hit. Without connected intelligence: that includes linking identity, device, and behavior signals, banks and account holders are exposing themselves to serious fraud risks.

The rise of AI-driven and social engineering aided fraud
Digital fraud is largely driven by AI and social engineering. Instead of stolen credentials, criminals are now deploying AI-generated voices and deepfake media that impersonate innocent account holders and decision-makers.
Unlike traditional fraud practices, AI-enabled tactics have a strong layer of credibility, which makes them even more dangerous and convincing to a layman user.
They usually take the form of:
Voice cloning: Scammers recreate the voices of decision-makers through publicly available audio. Using these spurious voices, they call up family members or sub-ordinates to make wire transfers or urgent payments.
AI-generated video: Using deepfake videos, fraudsters simulate the actions and mannerisms of actual users. Video snippets feature financial distress or payment requests that are channeled to fraudster-controlled accounts for siphoning off money.
Automated script creation: Fraudsters use AI to generate personalized scam messages at scale, targeting users who respond assuming they are original messages. For example, fake penalty intimation messages from government agencies with a link that redirects to a fake payment link.
Related Read: Social Engineering Tactics: Exploring the ‘Human’ Angle in Fraud
When OTPs and basic KYC are no longer strong defenses
Most banks send one-time passwords (OTPs) as multi-factor authentication checks (MFA) to prevent fraud. However, these controls are no longer strong defenses against users being manipulated into executing fraudulent transactions.
OTPs are futile against AI-based voice and text messages that mimic a real user.
Basic KYC checks focus more on verifying credibility of the documents rather than establishing the context or intent of the interaction.
Personal information scraped from online sources is sufficient to run scams that seem authentic, as if they are being used by the user themselves.
But, not all hope is lost. Banks are raising their defenses using behavioral and device intelligence. This threat insight helps differentiate normal users from fraudsters and stop a fraudulent transaction early in its tracks.
Related Read: Understanding Device Intelligence: How It Works and Its Importance in Fraud Prevention
Some of these risk signals include:
Behavior patterns: Unique personal traits of the user like typing speed, navigation paths, and interaction duration that vary from past patterns.
Device risk: Unusual device configurations, emulators, or varying device metadata at onboarding or login stage.
Network context: Access from unfamiliar IP ranges or via anonymization services like VPN that may indicate bot activity.
Risk-based authentication vs forced verification
Fraud and customer experience occupy two extreme sides of a scale. Authentication is placed right at the center of these two. Frictionless CX can increase fraud risk, while adding more checks can disrupt customer experience. However, despite the positive intent, additional verification may not prevent fraud and might even introduce more vulnerabilities.
Related Read: Risk-Based Authentication: How Can It Help Your Business?
At a high level, digital banks rely on two different approaches: forced verification and risk-based authentication. The difference between them can directly impact fraud losses, customer trust, and conversion rates.
Risk-based authentication | Forced authentication |
|---|---|
Evaluates risk in real time using context, behavior, and device signals | Applies the same verification steps to all users and sessions |
Only when risk increases or signals change | Every login, transaction, or rule-based event |
Low friction for trusted users | High friction for all users |
Improves onboarding and login completion | Increases drop-offs and abandonment |
Recognizes known users on known devices | Re-verifies users repeatedly |
How trusted device binding helps reduce unnecessary challenges
In the face of fraud and customer experience trade-off, the most effective friction-reduction strategy is trusted device binding.
When a bank can reliably recognize a customer’s device, it establishes a certain amount of trust that can be carried off across multiple sessions.
This allows the bank to:
Skip redundant challenges for identified devices.
Detect risky changes, such as device resets or use of emulators.
Flag account access from new or manipulated devices.
In short, device trust does not replace identity checks. It complements them by answering a different question: Is this interaction happening from a device or environment that is trustworthy?
Country and regulatory landscape
Fraud is border-agnostic. It doesn’t stop at GCC borders, nor does it restrict itself to one specific digital banking channel.
This universal applicability of fraud is forcing regulators to tighten controls around monitoring, traceability, and accountability. Especially in the GCC countries, the result is a regulatory landscape that is locally distinct, yet increasingly aligned in outcomes.
Here is a brief overview of the regulatory landscape at the two most prominent GCC countries: Saudi Arabia and UAE.
Saudi Arabia (SAMA): Transaction integrity at scale
Saudi Arabia has one of the fastest-growing digital payment ecosystems in the region. According to Saudi Central Bank (SAMA), in 2024, e-payments accounted for 79% of all retail payments. Instant payments, wallets, and rapid fintech growth are the key drivers behind this digital payment adoption.
SAMA’s regulatory framework is also fine-tuned to tackle this scale of transactions:
Real-time transaction monitoring across payments and transfers.
Strong Anti-Money Laundering (AML) and CTF (Counter-Terrorism Financing) alignment, especially for instant payments and remittances.
Growing emphasis on behavioral consistency and anomaly detection, not just static rules.
As transaction volume and velocity continue to increase, SAMA’s regulations are shifting from reactive controls to continuous monitoring. Banks are expected to explain what the decision was, as also why it was made and whether any earlier risk signals were ignored.
Related Read: Decoding KSA's SAMA Mandate
UAE: Digital identity, KYB, and open finance
The UAE’s regulatory approach is strongly leaning towards digital trust and ecosystem participation.
It is indicated by key developments such as:
National digital identity frameworks enabling remote onboarding and authentication.
Stricter KYB requirements for platforms, marketplaces, and payment intermediaries.
Expansion of open finance, increasing data sharing across regulated entities.
Cross-border fraud: A shared regional risk
It is evident that remittances and cross-border payments are a core part of the GCC economy. The region processes at least 30 billion dollars annually in outbound and inbound remittance flows, with Saudi Arabia and the UAE ranking among the world’s top remittance corridors.
This creates shared fraud challenges across the region, primary risks being:
Account and mule reuse across countries.
Scams initiated in one jurisdiction and executed in another.
Limited visibility when fraud signals sit in separate national systems.
Fraud patterns do not care for regulatory borders, but risk systems do. It is here that connected intelligence matters the most.
Why connected intelligence matters at regional scale
As GCC regulators raise expectations, the existing fragmented controls create blind spots. Connected intelligence can solve for this by linking:
Identity - Who the user is claiming to be.
Device - Which device they are using from and through which service.
Behavior - Individual actions and interactions over a period of time.
This connected intelligence helps detect fraud earlier, stop it from spreading across the region, and ultimately provide regulators with clear, auditable decision trails.
Why documents alone no longer establish trust
Document checks are essential for onboarding, but they were designed for a different threat model that was applicable at a different time period. The primary purpose of documentation is to confirm whether a document is real and pertains to the user who is applying for the service. They, however, have little control over how an account is used after approval, or whether the same identity is used by multiple accounts, devices, or sessions.
As fraud shifts toward fake identities and mule activity, one-time verification is an inadequate form of security.
Also, attackers have become adept at bypassing document-led controls using emulator farms, virtual cameras, and rooted or jailbroken devices. These environments can simulate the clean onboarding signals that fraud systems look for, while hiding automation and coordination of the bigger fraud network.
Once these accounts are active, the same devices and behavioral patterns often reappear across logins, payments, and transfers. Document checks fail to flag off these links because they operate in isolation and have limited relevance after onboarding.
Modern fraud prevention requires advanced techniques like device fingerprinting and graph-based detection to uncover these hidden connections.
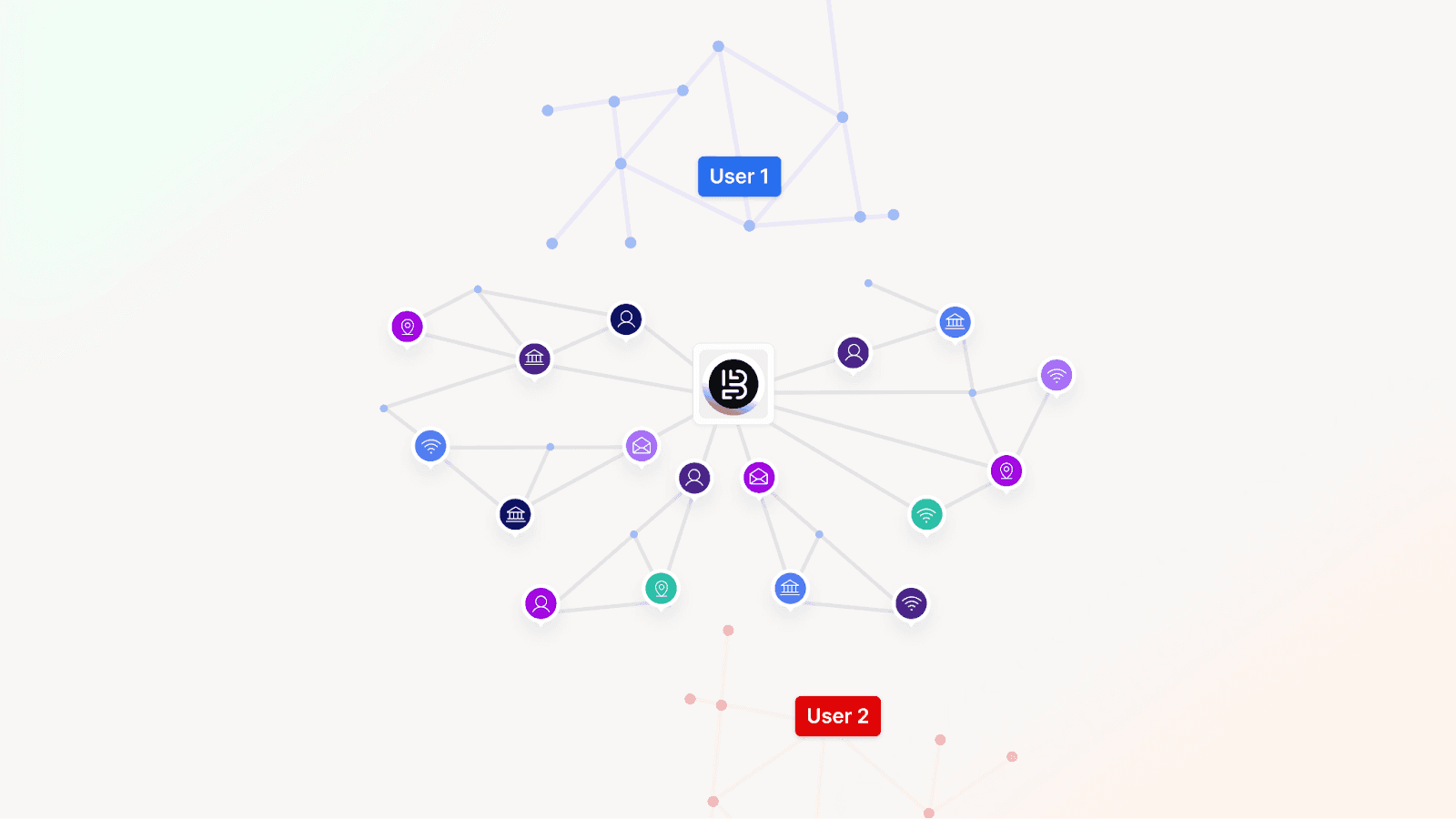
Device and behavior signals persist across time, products, and identities, allowing banks to identify shared infrastructure used to run a network of synthetic accounts and mule networks.
Related Read: A Food Delivery Company Eliminates a 2,700+ User Fraud Ring
This shifts trust from a single one-point checkpoint to a living, breathing risk signal.
Bureau believes one-time verification is inadequate to establish trust. It needs to be continuously observed, correlated, and re-evaluated as users interact with the system.
Rethinking build vs buy in Middle East fraud systems
As fraud risk grows more complex, banks in the Middle East are confronted with a binary choice. They can either choose to build large parts of their fraud stack in-house, or rely entirely on off-the-shelf platforms.
In practice, neither extreme works well. Building everything from ground-up internally slows down time-to-value and puts a heavy burden on engineering teams. Buying rigid systems restricts control and adaptability. Banking leaders have a third option: which is buying the foundation and building differentiation on top. This hybrid approach balances speed, compliance, and long-term flexibility without piling up technical debt or stretching resources.
Related Read: From In-House Tools to Unified Fraud Intelligence
Why a hybrid approach is the best bet for the Middle East
As discussed earlier, banks in the GCC operate under fast-moving regulatory expectations and high transaction volumes. Therefore, maintaining in-house device intelligence and fine-tuning it to stay abreast with evolving fraud tactics and compliance requirements can be a big ask. The build-on-top model helps ease the situation by supporting real-time risk decisioning based on variables like products, region, and customer preferences.
Dimension | Build in-house | Buy off-the-shelf | Buy the foundation, Build differentiation |
|---|---|---|---|
Time-to-value | Usually slow, taking anywhere from months or years | Fast initial rollout | Fast foundation with incremental gains |
Engineering effort | High ongoing cost for maintenance | Low upfront effort | Focused on value, not plumbing |
Fraud coverage | Narrow at launch, expands slowly | Broad but generic | Broad foundation with tailored controls |
Device & behavioral intelligence | Complex to build and maintain | Often opaque or limited | Provided as a core layer, extensible |
Compliance readiness | Heavy internal burden | Depends on vendor transparency | Shared responsibility with clear auditability |
Adaptability to new fraud | High, but resource-intensive | Limited by vendor roadmap | High, with internal control |
Operational drag | Increases over time | Hidden constraints emerge | Kept low by design |
Regional scalability | Difficult to replicate across geos | One-size-fits-all | Designed for multi-country use |
Fraud prevention in 2026 in the Middle East
In 2026 and beyond, fraud prevention in the Middle East will be defined by the continuity of transactions and not static checks. Risk decisions will not be restricted to standalone junctures like onboarding or payment approval. Banks will have always-on risk monitoring that pan the full customer lifecycle.
Related Read: Onboarding Trusted Users at Scale with Bureau
However, this shift calls for a major upgrade in risk decisioning. Siloed tools will have to make way for connected intelligence that can connect the dots and explain risk clearly. The goal is not to have more alerts or controls, but to unearth blind spots faster and make decisions confidently.
Fraud prevention will no longer be restricted to a collection of tools. It will evolve into a connected system that observes trust continuously, adapts to change, and scales across products, users, and even borders.
Move from isolated controls to connected risk intelligence.See how Bureau provides always-on monitoring and improves fraud detection across onboarding, login, and transactions. |
TABLE OF CONTENTS
See More
Recommended Blogs
Landing Page.
Simple, bold.
Sign Up
Download

Products
Solutions
Resources
© 2026 Bureau . All rights reserved.
Solutions
Industries
Resources
Company
Solutions
Industries
Resources
Company
© 2026 Bureau . All rights reserved.
Follow Us
Leave behind fragmented tools. Stop fraud rings, cut false declines, and deliver secure digital journeys at scale
Our Presence











Leave behind fragmented tools. Stop fraud rings, cut false declines, and deliver secure digital journeys at scale
Our Presence











© 2026 Bureau . All rights reserved.




