Compare Top Account Takeover Prevention Software and Build a Full-Stack ATO Defense
Compare Top Account Takeover Prevention Software and Build a Full-Stack ATO Defense
Compare Top Account Takeover Prevention Software and Build a Full-Stack ATO Defense
Explore top account takeover prevention tools and learn how to deploy device intelligence, biometrics, and risk scoring to stop ATO attacks in real time.
Author
Team Bureau



See how Bureau has helped industry leaders defend against networked Industrial-scale frauds →
Schedule a Demo
TABLE OF CONTENTS
See Less
Most attacks don’t break authentication; they use valid credentials and move through sessions undetected. Bureau ID’s 2026 India Fraud Report found that India’s UPI ecosystem processed 228 billion transactions worth ₹300 trillion in 2025, creating a massive attack surface for real-time digital fraud. That scale makes passwords and OTPs insufficient on their own, especially when attackers already control valid credentials.
The impact also shows up directly in business risk. The FTC reported $12.5 billion in fraud losses in 2024, which shows how quickly these attacks translate into financial damage.
Account takeover prevention software addresses this problem. Instead of relying on passwords or OTPs, these systems detect risk using device intelligence, behavioral signals, and real-time decisioning, even when access looks legitimate.
In this guide, we’ll break down the best account takeover prevention software in 2026, how these tools differ, and our evaluation process. You’ll also learn how to deploy ATO protection to catch fraud earlier, protect revenue, and preserve user trust without adding friction in the process.
Quick Comparison: Top 6 Account Takeover Prevention Software
Account takeover prevention software detects and stops unauthorized access to user accounts. It analyzes login behavior, device signals, and credentials in real time. The software blocks bots, credential stuffing, and suspicious sessions, using adaptive authentication and risk scoring to verify users without adding friction.
Businesses use these tools to protect accounts, prevent fraud, and reduce account compromise across banking, fintech, and ecommerce platforms.
Let’s look at a quick comparison of the top 6 tools.
Tool | Core strength | ATO capability | Lifecycle coverage | Primary signals used | Ease of deployment | Pricing model |
Bureau ID | Unified risk decisioning + network fraud prevention | Full-lifecycle ATO prevention | Onboarding, login, session, and transactions | Device, behavior, identity, network, and transaction signals | High: No-code workflows, APIs, SDKs, and one orchestration layer | Custom enterprise |
BioCatch | Behavioral biometrics | Session-level ATO detection | Login and live session activity | Behavioral biometrics and session behavior | Moderate: Requires integration into digital banking journeys | Enterprise + usage |
Featurespace | Anomaly detection | Post-login transaction monitoring | Post-login transactions | Transaction behavior and anomaly models | Moderate to complex: Suited to enterprise banking systems | Enterprise license |
Sift | Fraud detection models | Post-login ATO monitoring | Login, profile changes, and transactions | User behavior, transaction signals, and cross-account patterns | Moderate: Built for high-volume digital platforms | Usage-based |
Riskified | Transaction risk | ATO tied to payments | Checkout and payment flows | Purchase behavior, order data, and transaction risk | Moderate to high: Strongest when tied to e-commerce payment flows | Revenue-share |
Kount | Device intelligence | Login and post-login fraud detection | Login, device activity, and transactions | Device intelligence, identity signals, and transaction data | Moderate: Works well where device and payment signals matter | Tiered + usage |
Each tool approaches ATO prevention differently. While some focus on behavioral signals, others specialize in transactions or device intelligence. The right choice depends on where fraud appears in your user journey.
How We Evaluated The Top Account Takeover Prevention Tools
We evaluated these account takeover prevention software tools based on how well they help businesses detect risk across the user journey, not just at login. Since modern ATO attacks can move across onboarding, credentials, sessions, account changes, and transactions, we prioritized tools that offer strong signal coverage, real-time decisioning, and practical deployment options.
The key factors we considered were:
ATO coverage: Whether the tool supports login protection, session monitoring, transaction risk, or full-lifecycle account takeover prevention.
Primary detection signals: The strength of device intelligence, behavioral biometrics, identity signals, transaction patterns, and network intelligence.
Use-case fit: Whether the platform is better suited for digital banks, fintechs, marketplaces, ecommerce businesses, or large financial institutions.
Ease of deployment: Whether the tool offers APIs, SDKs, no-code workflows, or requires deeper enterprise integration.
Friction control: How well the platform helps teams detect fraud without forcing unnecessary verification on genuine users.
This approach helps compare each tool based on practical buying criteria, not just feature lists. It also makes the comparison more useful for teams that need to stop account takeover without hurting conversion, customer trust, or day-to-day operations.
Best Account Takeover Prevention Software in 2026
1. Bureau ID
Bureau ID is an AI-powered unified risk decisioning platform designed to prevent account takeover across the entire user lifecycle, from onboarding to login, session activity, and transactions. The platform combines device intelligence, behavioral biometrics, identity signals, and network data into a single decision layer.
This unified approach helps detect fraud even when credentials appear valid and enables real-time, low-friction decisioning at scale.
Key strengths:
Full lifecycle coverage: Bureau ID helps detect ATO across onboarding, login, session, and transactions, which reduces blind spots where fraud typically slips through.
Unified decisioning layer: The platform combines device, behavior, identity, network, and transaction signals into one risk score, improving accuracy and speeding up decision-making.
Device intelligence layer: It identifies devices at the first point of interaction and evaluates signals such as spoofing, emulators, repeat device usage, and SIM swap indicators, helping teams detect suspicious access before fraud reaches the session or transaction stage.
No-code workflows: Bureau ID lets teams configure rules and verification flows without engineering dependency, speeding up response to new fraud patterns.
Real-time detection: It delivers risk decisions in milliseconds and continuously improves with feedback loops to help teams stay ahead of evolving attack methods.
Graph identity intelligence: It allows you to map connections across accounts to uncover fraud rings and mule networks, helping detect coordinated attacks that look clean in isolation.
In fact, Bureau ID has a dedicated Graph Identity Network to detect money mules and fight hidden fraud rings. For instance, they helped eliminate a major fraud ring for a large food delivery platform using the Graph Identity Network.
How Bureau ID Helped Eliminate a 2,700-Account Fraud Ring
Client problem: A food delivery platform faced a large-scale fraud ring operating across 2,700 accounts. Traditional systems flagged suspicious activity at the individual account level, which slowed down detection and response. Fraudsters continued exploiting the platform by creating and managing multiple linked accounts that appeared legitimate in isolation.
Bureau ID’s implementation:
Mapped relationships across accounts using shared devices, phone numbers, and behavioral patterns.
Used the Graph Identity Network to identify hidden connections between seemingly independent users.
Applied device intelligence to detect repeat offenders across sessions and devices.
Analyzed behavioral signals to distinguish coordinated fraud activity from genuine users.
Unified all signals into a single decisioning layer for faster detection.
Results:
A 2,700+ user fraud ring operating through 150 devices was mapped and blocked.
1,750+ accounts from just 3 devices were removed, eliminating high-abuse vectors.
97% of collusive users with high-risk scores were flagged for further investigation.
Repeat offenders were identified and blocked, preventing future fraud attempts.
Fraud reduction was observed within days of deployment.
You can read the full case study here → Food Delivery Company Eliminates a 2,700+ User Fraud Ring
Bureau ID works best for fintech, digital banks, and high-transaction platforms that need end-to-end ATO prevention without adding friction to the user experience. Although it comes at a higher price point, its broader feature set and full-lifecycle fraud coverage can make it a stronger long-term investment for businesses that need comprehensive account takeover prevention.
If you are evaluating solutions that combine identity, device, and behavioral signals into a single system, schedule a demo today and explore how Bureau ID fits your fraud prevention strategy.
2. BioCatch
BioCatch specializes in behavioral biometrics for post-login fraud detection.
The platform analyzes over 2,000 behavioral parameters: typing cadence, mouse movements, pressure, hand tremors, navigation flow, and device orientation to identify compromised accounts during active sessions, even when attackers use valid credentials.
Key strengths:
Exceptional at detecting sophisticated fraud: Analyzes thousands of interactions per session using advanced behavioral modeling to distinguish genuine users from remote access tool (RAT) attacks, bots, and manual account takeover attempts.
Real-time session monitoring with adaptive response: Continuously evaluates behavioral risk during active sessions and triggers step-up authentication when patterns deviate from normal, delivering real-time alerts.
Advanced bot and automation detection: Effectively identifies scripted attacks, automated credential stuffing tools, and organized fraud operations using behavioral signals during session activity
Banking-grade platform with expert support: Built for regulated financial institutions with PSD2 Strong Customer Authentication (SCA) compliance capabilities
While BioCatch delivers strong behavioral biometric capabilities, there are a few implementation and resource considerations to evaluate:
The platform works as an integrated layer within existing authentication systems rather than a standalone tool.
And implementation typically requires 30-60 days of baseline behavioral profiling per user to build accurate detection models, which can get complex for organizations with diverse user systems.
Pricing tends to run high and scales with usage, making it better suited for larger organizations with enterprise budgets.
Best for: Large banks that prioritize deep behavioral biometric analysis at the session level.
3. Featurespace
Featurespace is built for fraud and financial crime teams that need advanced anomaly detection, especially in banking and transaction-heavy environments.
Its ARIC Risk Hub uses adaptive behavioral analytics and machine learning to detect scams, account takeovers, card fraud, payment fraud, and suspicious transaction patterns in real time. Featurespace is especially strong where post-login risk and transaction monitoring matter most.
Key strengths:
Strong anomaly detection for financial crime: Uses adaptive behavioral analytics to identify unusual customer and transaction behavior, helping fraud teams detect activity that static rules may miss.
Real-time transaction monitoring: Designed to monitor financial events as they happen, which makes it useful for detecting suspicious post-login activity, payment fraud, and account misuse.
Banking and regulated-market focus: Built for financial institutions that need fraud detection and financial crime prevention within controlled, compliance-heavy environments.
False-positive reduction: Publicly states that its platform has helped reduce false positive alerts by 75%, which is valuable for teams dealing with heavy alert volumes.
Enterprise risk decisioning: Its ARIC Risk Hub functions as a centralized risk decision engine for fraud and AML use cases, which helps large institutions bring multiple risk workflows into one environment.
While Featurespace is strong for anomaly detection and transaction monitoring, there are a few fit considerations to evaluate:
The platform is best suited for organizations that already have mature fraud operations and enough transaction data to support enterprise risk models.
It is also more focused on post-login and transaction-level risk, so teams looking for full-lifecycle ATO prevention across onboarding, device intelligence, identity risk, and session behavior may still need broader coverage.
Best for: Large banks and financial institutions that focus on post-login transactions.
4. Sift
Sift is a digital fraud prevention platform that helps businesses detect account takeover, payment fraud, policy abuse, and other forms of online risk. Its platform is powered by a global data network of around 1 trillion annual events across 700+ brands, which helps teams identify suspicious behavior across users, accounts, and transactions at scale.
Key strengths:
Broad digital fraud coverage: Covers account takeover, payment fraud, and first-party abuse, which makes it useful for digital businesses that want one platform for multiple fraud use cases.
Cross-account intelligence: Connects user, account, and transaction signals to help detect coordinated fraud patterns across large digital ecosystems.
Real-time risk decisioning: Evaluates risk quickly across user journeys, helping teams stop suspicious activity before it turns into financial or reputational damage.
Strong marketplace and platform fit: Works well for online marketplaces, SaaS platforms, and high-volume digital businesses where fraud often moves across accounts, payments, and policy abuse.
Machine learning and behavioral analysis: Sift’s ATO prevention uses machine learning and behavioral analysis to detect fraudulent logins and compare activity with patterns of good and bad behavior.
While Sift offers strong cross-account fraud detection, teams should evaluate where they need the most protection:
Its strength is broad digital fraud monitoring across login, account changes, transactions, and abuse patterns.
Sift’s broader fraud coverage can be useful, but teams may need careful configuration to avoid noisy rules or unnecessary reviews.
For businesses that need deeper identity verification, device-first risk detection, and lifecycle orchestration from onboarding through transactions, a more unified risk decisioning platform may be a better fit.
Best for: Marketplaces, SaaS platforms, and digital businesses that need post-login ATO monitoring.
5. Riskified
Riskified is an e-commerce-focused fraud prevention platform built around transaction risk, chargeback protection, and account security. Its Account Secure solution helps merchants detect account takeover attempts at login and checkout by comparing current sessions with past account-owner behavior and issuing allow, notify, or challenge decisions.
Key strengths:
Strong ecommerce fraud focus: Built for online merchants that need to protect checkout flows, reduce chargebacks, and approve more legitimate orders.
ATO protection tied to commerce journeys: Its Account Secure product helps detect malicious login attempts, credential-stuffing bots, and suspicious account activity in retail and ecommerce environments.
Transaction history as a risk signal: Uses transaction history from the merchant and its wider merchant network to improve account-risk decisions.
Chargeback protection: Riskified’s Chargeback Guarantee helps merchants reduce fraud-related chargeback exposure, which is especially valuable for high-volume ecommerce brands.
While Riskified is strong for e-commerce fraud and chargeback protection, there are a few scope and fit considerations to evaluate:
The platform is primarily commerce-oriented, so its strongest fit is checkout, transaction risk, and account protection tied to purchase journeys.
Teams that need ATO prevention before checkout, such as onboarding fraud, identity takeover, or session hijacking detection, may need broader lifecycle coverage.
Riskified’s value is closely tied to e-commerce transaction volume, which may make it less relevant for fintech, digital banking, or non-commerce platforms.
Best for: E-commerce brands and online retailers that need ATO tied to payments and chargeback management.
6. Kount
Kount, an Equifax company, provides fraud prevention capabilities across account protection, new account fraud, payments, and digital trust. Its account protection solution helps prevent login fraud, fake account creation, and takeover fraud using device, email, phone, address, AI, machine learning, reporting, and analytics signals.
Key strengths:
Device intelligence foundation: Kount uses device and identity signals to identify suspicious activity, repeat offenders, and risky account behavior across digital journeys.
Account protection coverage: Kount 360 Account Protection supports login protection, new account fraud prevention, and account takeover prevention.
Customizable fraud policies: Kount allows merchants to manage, customize, and adjust account takeover policies inside the platform without heavy development requirements.
Real-time reporting: Kount Control supports reporting on failed login attempts, risky IP addresses, compromised accounts, and other inbound anomalies.
Retail and e-commerce alignment: Kount is especially relevant for businesses that need to detect fake accounts, promo abuse, card testing, and repeat fraud behavior across digital commerce flows.
While Kount offers practical device-led fraud prevention, there are a few signal and coverage considerations to evaluate:
Behavioral biometrics are not its core signal, so teams needing deep session-level behavior analysis may need additional coverage.
Businesses with complex identity-risk needs may need to assess whether Kount provides enough context across linked accounts, mule networks, and coordinated fraud rings.
For teams looking for a single system across onboarding, login, session behavior, and transactions, Kount may need to work alongside other fraud and identity tools
Best for: E-commerce and retail businesses that focus on login and post-login fraud detection.
How Does Bureau ID Help With ATO?
Most tools tend to focus on a single layer of the fraud lifecycle, which often leaves gaps that attackers exploit.
In fact, Bureau ID's 2026 India Fraud Report found that 48% of Indian enterprises identify mule networks as the most difficult fraud threat to detect and control, ahead of phishing, synthetic identities, account takeover, and social engineering.
That finding matters for ATO because compromised accounts often become part of wider fraud networks, which are difficult to detect when each account is reviewed in isolation.
Bureau ID takes a more connected approach by bringing together device, identity, behavioral, and transaction signals into a single system, enabling continuous risk evaluation across the entire user journey.
Step 1: Device Intelligence
Bureau ID starts by identifying the device at the very first interaction. Instead of waiting for login attempts, the platform evaluates signals such as device configuration, spoofing attempts, emulator usage, and SIM swap indicators early in the journey.
This early visibility helps flag suspicious activity before credentials even come into play, which reduces reliance on passwords as the primary line of defense.
Step 2: Identity Verification
Once the device is assessed, the platform connects the user to a broader identity context. Bureau ID cross-references signals against its identity graph, which helps surface shared devices, linked accounts, and unusual identity patterns.
This approach shifts detection from looking at individual users in isolation to understanding how they connect within larger fraud networks.
Step 3: Behavioral Biometrics
As the session progresses, behavioral biometrics add another layer of insight. Bureau ID continuously monitors how users interact with the platform, including navigation flow, interaction speed, and usage patterns.
These signals help distinguish genuine users from bots, scripted attacks, or remote access tools that often mimic normal activity but fail to replicate natural behavior.
Step 4: Real-Time Risk Decisioning
Security teams describe seeing more account takeovers tied to token theft and phishing kits that make MFA bypass easier. That practitioner-level concern supports why ATO prevention cannot stop at login or OTP checks; risk needs to be evaluated across devices, sessions, and account activity.
All of these signals come together in a unified decisioning layer. Bureau ID evaluates risk in real time and assigns a score based on the combined context of device, identity, and behavior. Instead of applying blanket verification methods, the system triggers adaptive authentication only when the risk level warrants intervention.
This ensures that genuine users move smoothly while suspicious activity faces appropriate friction.
Step 5: Continuous Monitoring and Feedback
Detection does not stop after login. Bureau ID continues to monitor activity across sessions, transactions, and account changes. These signals feed back into the system, which allows risk models to evolve and improve over time.
This continuous loop helps reduce false positives while strengthening detection accuracy as new fraud patterns emerge.
When these layers work together, account takeover detection starts to understand behavior across the full lifecycle, allowing businesses to move from reactive fraud handling to proactive prevention, without compromising the user experience.
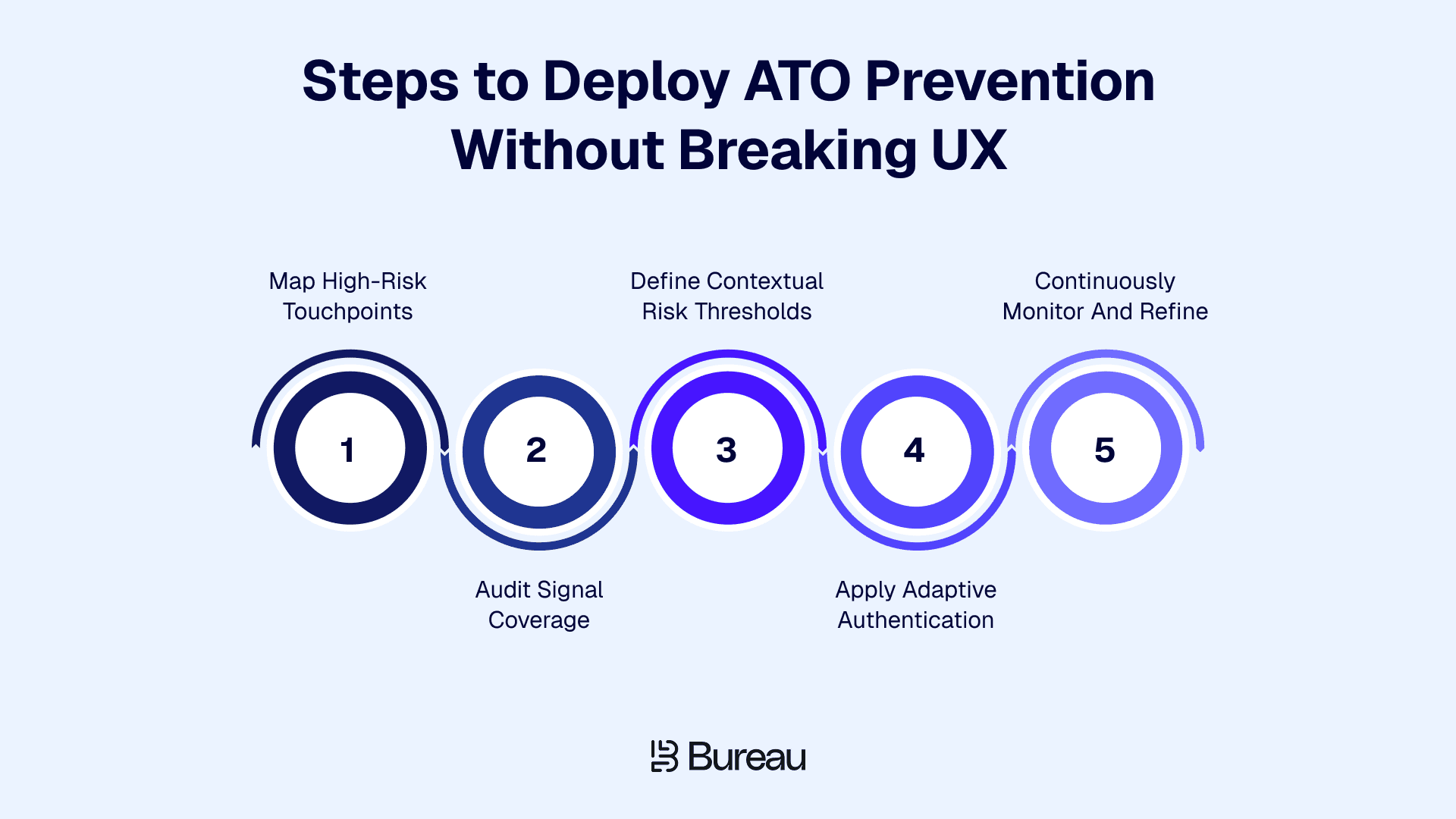
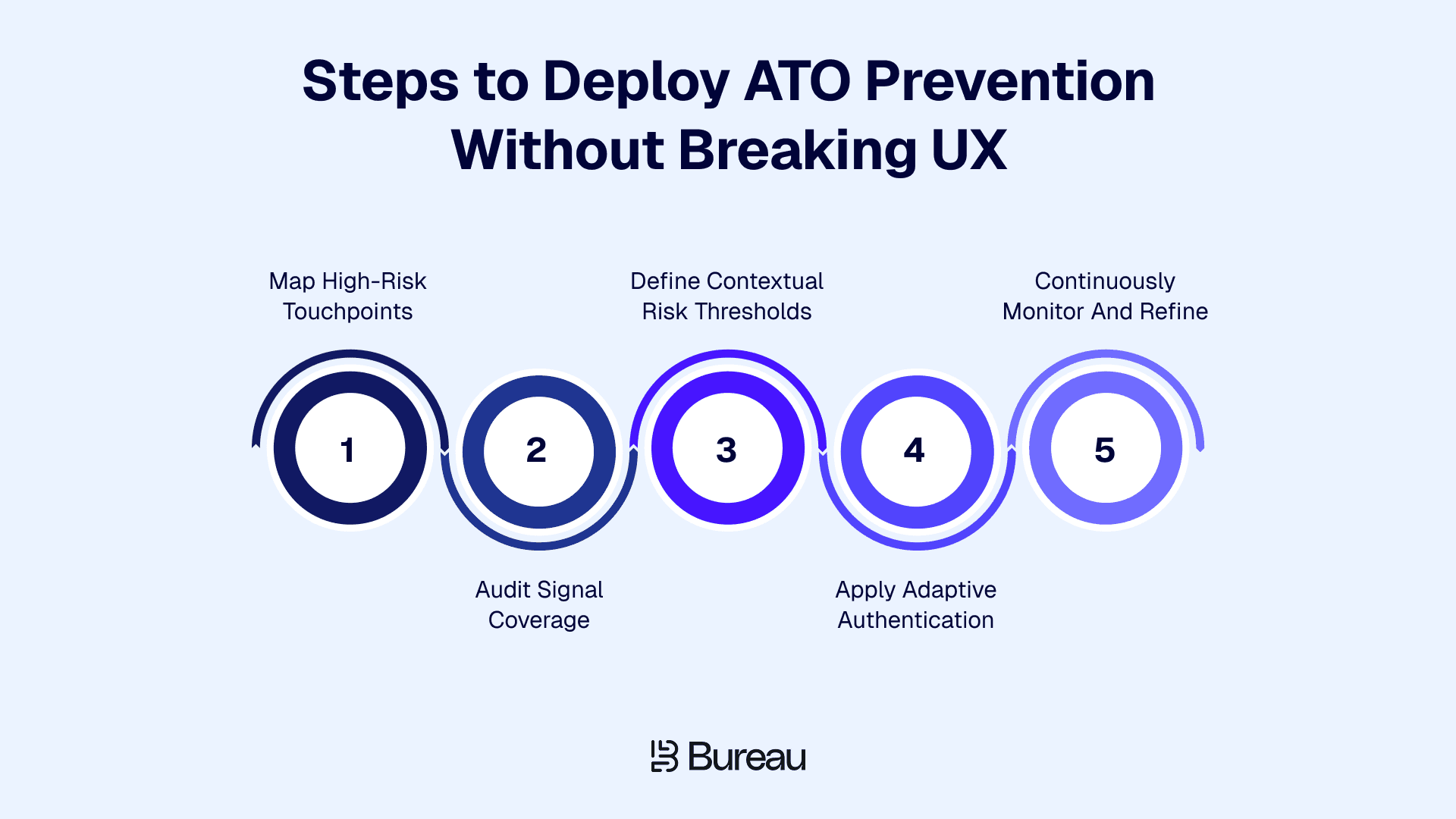
Implementation Framework: How to Deploy ATO Prevention Without Breaking UX?
Most teams run into the same trade-off sooner or later. The moment security gets stricter, user experience starts to suffer. More friction leads to higher drop-offs, abandoned sessions, and frustrated users. The challenge is designing a system where both security and experience work together.
This balance matters because fragmented controls make fraud harder to catch early. Bureau ID’s UK and EU Fraud Report found that 67% of organizations say siloed systems prevent early signal correlation, while 50% faced device spoofing and emulator-based activity. That makes a strong case for ATO prevention that connects identity, device, behavior, and transaction signals before adding more friction.
A practical way to approach this is to break the problem down across the user journey instead of treating ATO as a single checkpoint.
Start by mapping high-risk points across the journey: Not every stage carries the same level of risk, and treating them equally often leads to unnecessary friction. Focus on areas where fraud typically shows up:
Onboarding flows where fake or synthetic identities enter the system
Login attempts, especially from new or unrecognized devices
Password resets and account recovery flows, which attackers often exploit
Transactions or account changes that involve financial or sensitive actions
Once these touchpoints are clear, the next step is to understand what signals you actually have in place.
Audit your signal coverage before adding new controls: Many systems rely heavily on credentials or OTPs (one-time passwords), which creates blind spots once those signals are compromised. A more complete setup includes:
Device intelligence to identify spoofing, emulators, and repeat offenders
Behavioral analytics to track how users interact during sessions
Identity signals that connect users across accounts and environments
Gaps in any of these areas often explain why fraud bypasses existing defenses.
Define risk thresholds based on context, not assumptions: A login from a trusted device should not trigger the same response as one from a new location or unfamiliar device. Risk needs to be evaluated per action:
Low-risk activity should move forward without interruption
Medium-risk activity may require light verification
High-risk activity should trigger stronger step-up checks
This layered approach prevents over-securing routine actions while still catching suspicious behavior.
Apply adaptive authentication with precision: Instead of enforcing MFA across every interaction, apply it only when risk signals justify it. This reduces unnecessary friction and keeps genuine users moving through the flow without disruption. The goal is to challenge only when something feels off, not by default.
Continuously monitor and refine detection models: ATO prevention does not end at login. Fraud patterns evolve quickly, and detection systems need to adapt just as fast. Continuous monitoring helps teams:
Track session behavior and post-login activity
Identify false positives and refine thresholds
Adjust rules without long development cycles, especially with no-code workflows
Over time, this feedback loop improves both detection accuracy and user experience.
The core idea behind this framework is simple. Precision matters more than restriction, and the systems that succeed are the ones that apply friction selectively rather than universally. When detection aligns with real user behavior, security changes from a barrier to an invisible layer that works exactly when it should.
Related Read: The Key Reasons Fraud Continues to Outpace Defenses in the UK and EU
Build a Defense That Covers the Full Journey
Basic ATO defenses solve one part of the journey, but attackers do not operate that simply. They move across onboarding, login, sessions, account changes, and payments until they find the weakest point.
The next step is to evaluate whether your current setup connects device intelligence, behavioral signals, identity context, and real-time risk decisioning in one place. If those signals sit across separate tools, your team may still miss the patterns that reveal coordinated fraud.
When you work with Bureau ID, the team can help you assess where ATO risk appears in your user journey, which signals you already capture, and where fraud may be slipping through. From there, they can help you build a risk decisioning flow that applies friction only when needed, while letting genuine users move forward smoothly.
If you are ready to move from isolated fraud checks to full-journey ATO prevention, schedule a demo with Bureau ID and see how its unified risk decisioning platform can support your account takeover prevention strategy.
FAQs
1. What is account takeover prevention software?
Account takeover prevention software protects user accounts from unauthorized access. The software detects suspicious logins, stolen credentials, and bot-driven attacks in real time. The system analyzes device signals, user behavior, and session activity to identify anomalies. The goal is to stop fraud before attackers gain control of accounts.
2. What are the best account takeover prevention software tools?
Top account takeover prevention software tools include Bureau ID, BioCatch, Featurespace, Sift, Riskified, and Kount. These platforms focus on different strengths such as behavioral biometrics, fraud analytics, device intelligence, and real-time risk decisioning. Businesses compare these tools based on detection accuracy, integration, scalability, and ability to reduce fraud without increasing login friction.
3. Why is Bureau ID a strong option for account takeover prevention?
Bureau ID offers a multi-layered approach to account takeover prevention. The platform combines device intelligence, identity verification, behavioral biometrics, and real-time risk decisioning. This approach helps detect suspicious activity early and block unauthorized access. Continuous monitoring improves detection over time. The system focuses on reducing fraud while maintaining a smooth user experience.
4. How does account takeover prevention software work?
Account takeover prevention software analyzes login activity, device signals, and user behavior. The system assigns risk scores based on anomalies such as unusual locations or rapid login attempts. High-risk sessions trigger adaptive authentication. Continuous monitoring tracks session activity to detect hijacking or unauthorized changes.
5. Can account takeover prevention software stop bot attacks and credential stuffing?
Account takeover prevention software detects and blocks automated login attempts. The system identifies patterns such as rapid login requests, reused credentials, and abnormal traffic. Bot detection and credential intelligence help prevent large-scale credential-stuffing attacks before accounts are compromised.
6. How does account takeover prevention software protect accounts without adding login friction?
Account takeover prevention software uses adaptive authentication and risk-based controls. Low-risk users access accounts without interruption. High-risk activity triggers additional verification. Behavioral analytics and device recognition help maintain security while minimizing unnecessary login challenges.
Most attacks don’t break authentication; they use valid credentials and move through sessions undetected. Bureau ID’s 2026 India Fraud Report found that India’s UPI ecosystem processed 228 billion transactions worth ₹300 trillion in 2025, creating a massive attack surface for real-time digital fraud. That scale makes passwords and OTPs insufficient on their own, especially when attackers already control valid credentials.
The impact also shows up directly in business risk. The FTC reported $12.5 billion in fraud losses in 2024, which shows how quickly these attacks translate into financial damage.
Account takeover prevention software addresses this problem. Instead of relying on passwords or OTPs, these systems detect risk using device intelligence, behavioral signals, and real-time decisioning, even when access looks legitimate.
In this guide, we’ll break down the best account takeover prevention software in 2026, how these tools differ, and our evaluation process. You’ll also learn how to deploy ATO protection to catch fraud earlier, protect revenue, and preserve user trust without adding friction in the process.
Quick Comparison: Top 6 Account Takeover Prevention Software
Account takeover prevention software detects and stops unauthorized access to user accounts. It analyzes login behavior, device signals, and credentials in real time. The software blocks bots, credential stuffing, and suspicious sessions, using adaptive authentication and risk scoring to verify users without adding friction.
Businesses use these tools to protect accounts, prevent fraud, and reduce account compromise across banking, fintech, and ecommerce platforms.
Let’s look at a quick comparison of the top 6 tools.
Tool | Core strength | ATO capability | Lifecycle coverage | Primary signals used | Ease of deployment | Pricing model |
Bureau ID | Unified risk decisioning + network fraud prevention | Full-lifecycle ATO prevention | Onboarding, login, session, and transactions | Device, behavior, identity, network, and transaction signals | High: No-code workflows, APIs, SDKs, and one orchestration layer | Custom enterprise |
BioCatch | Behavioral biometrics | Session-level ATO detection | Login and live session activity | Behavioral biometrics and session behavior | Moderate: Requires integration into digital banking journeys | Enterprise + usage |
Featurespace | Anomaly detection | Post-login transaction monitoring | Post-login transactions | Transaction behavior and anomaly models | Moderate to complex: Suited to enterprise banking systems | Enterprise license |
Sift | Fraud detection models | Post-login ATO monitoring | Login, profile changes, and transactions | User behavior, transaction signals, and cross-account patterns | Moderate: Built for high-volume digital platforms | Usage-based |
Riskified | Transaction risk | ATO tied to payments | Checkout and payment flows | Purchase behavior, order data, and transaction risk | Moderate to high: Strongest when tied to e-commerce payment flows | Revenue-share |
Kount | Device intelligence | Login and post-login fraud detection | Login, device activity, and transactions | Device intelligence, identity signals, and transaction data | Moderate: Works well where device and payment signals matter | Tiered + usage |
Each tool approaches ATO prevention differently. While some focus on behavioral signals, others specialize in transactions or device intelligence. The right choice depends on where fraud appears in your user journey.
How We Evaluated The Top Account Takeover Prevention Tools
We evaluated these account takeover prevention software tools based on how well they help businesses detect risk across the user journey, not just at login. Since modern ATO attacks can move across onboarding, credentials, sessions, account changes, and transactions, we prioritized tools that offer strong signal coverage, real-time decisioning, and practical deployment options.
The key factors we considered were:
ATO coverage: Whether the tool supports login protection, session monitoring, transaction risk, or full-lifecycle account takeover prevention.
Primary detection signals: The strength of device intelligence, behavioral biometrics, identity signals, transaction patterns, and network intelligence.
Use-case fit: Whether the platform is better suited for digital banks, fintechs, marketplaces, ecommerce businesses, or large financial institutions.
Ease of deployment: Whether the tool offers APIs, SDKs, no-code workflows, or requires deeper enterprise integration.
Friction control: How well the platform helps teams detect fraud without forcing unnecessary verification on genuine users.
This approach helps compare each tool based on practical buying criteria, not just feature lists. It also makes the comparison more useful for teams that need to stop account takeover without hurting conversion, customer trust, or day-to-day operations.
Best Account Takeover Prevention Software in 2026
1. Bureau ID
Bureau ID is an AI-powered unified risk decisioning platform designed to prevent account takeover across the entire user lifecycle, from onboarding to login, session activity, and transactions. The platform combines device intelligence, behavioral biometrics, identity signals, and network data into a single decision layer.
This unified approach helps detect fraud even when credentials appear valid and enables real-time, low-friction decisioning at scale.
Key strengths:
Full lifecycle coverage: Bureau ID helps detect ATO across onboarding, login, session, and transactions, which reduces blind spots where fraud typically slips through.
Unified decisioning layer: The platform combines device, behavior, identity, network, and transaction signals into one risk score, improving accuracy and speeding up decision-making.
Device intelligence layer: It identifies devices at the first point of interaction and evaluates signals such as spoofing, emulators, repeat device usage, and SIM swap indicators, helping teams detect suspicious access before fraud reaches the session or transaction stage.
No-code workflows: Bureau ID lets teams configure rules and verification flows without engineering dependency, speeding up response to new fraud patterns.
Real-time detection: It delivers risk decisions in milliseconds and continuously improves with feedback loops to help teams stay ahead of evolving attack methods.
Graph identity intelligence: It allows you to map connections across accounts to uncover fraud rings and mule networks, helping detect coordinated attacks that look clean in isolation.
In fact, Bureau ID has a dedicated Graph Identity Network to detect money mules and fight hidden fraud rings. For instance, they helped eliminate a major fraud ring for a large food delivery platform using the Graph Identity Network.
How Bureau ID Helped Eliminate a 2,700-Account Fraud Ring
Client problem: A food delivery platform faced a large-scale fraud ring operating across 2,700 accounts. Traditional systems flagged suspicious activity at the individual account level, which slowed down detection and response. Fraudsters continued exploiting the platform by creating and managing multiple linked accounts that appeared legitimate in isolation.
Bureau ID’s implementation:
Mapped relationships across accounts using shared devices, phone numbers, and behavioral patterns.
Used the Graph Identity Network to identify hidden connections between seemingly independent users.
Applied device intelligence to detect repeat offenders across sessions and devices.
Analyzed behavioral signals to distinguish coordinated fraud activity from genuine users.
Unified all signals into a single decisioning layer for faster detection.
Results:
A 2,700+ user fraud ring operating through 150 devices was mapped and blocked.
1,750+ accounts from just 3 devices were removed, eliminating high-abuse vectors.
97% of collusive users with high-risk scores were flagged for further investigation.
Repeat offenders were identified and blocked, preventing future fraud attempts.
Fraud reduction was observed within days of deployment.
You can read the full case study here → Food Delivery Company Eliminates a 2,700+ User Fraud Ring
Bureau ID works best for fintech, digital banks, and high-transaction platforms that need end-to-end ATO prevention without adding friction to the user experience. Although it comes at a higher price point, its broader feature set and full-lifecycle fraud coverage can make it a stronger long-term investment for businesses that need comprehensive account takeover prevention.
If you are evaluating solutions that combine identity, device, and behavioral signals into a single system, schedule a demo today and explore how Bureau ID fits your fraud prevention strategy.
2. BioCatch
BioCatch specializes in behavioral biometrics for post-login fraud detection.
The platform analyzes over 2,000 behavioral parameters: typing cadence, mouse movements, pressure, hand tremors, navigation flow, and device orientation to identify compromised accounts during active sessions, even when attackers use valid credentials.
Key strengths:
Exceptional at detecting sophisticated fraud: Analyzes thousands of interactions per session using advanced behavioral modeling to distinguish genuine users from remote access tool (RAT) attacks, bots, and manual account takeover attempts.
Real-time session monitoring with adaptive response: Continuously evaluates behavioral risk during active sessions and triggers step-up authentication when patterns deviate from normal, delivering real-time alerts.
Advanced bot and automation detection: Effectively identifies scripted attacks, automated credential stuffing tools, and organized fraud operations using behavioral signals during session activity
Banking-grade platform with expert support: Built for regulated financial institutions with PSD2 Strong Customer Authentication (SCA) compliance capabilities
While BioCatch delivers strong behavioral biometric capabilities, there are a few implementation and resource considerations to evaluate:
The platform works as an integrated layer within existing authentication systems rather than a standalone tool.
And implementation typically requires 30-60 days of baseline behavioral profiling per user to build accurate detection models, which can get complex for organizations with diverse user systems.
Pricing tends to run high and scales with usage, making it better suited for larger organizations with enterprise budgets.
Best for: Large banks that prioritize deep behavioral biometric analysis at the session level.
3. Featurespace
Featurespace is built for fraud and financial crime teams that need advanced anomaly detection, especially in banking and transaction-heavy environments.
Its ARIC Risk Hub uses adaptive behavioral analytics and machine learning to detect scams, account takeovers, card fraud, payment fraud, and suspicious transaction patterns in real time. Featurespace is especially strong where post-login risk and transaction monitoring matter most.
Key strengths:
Strong anomaly detection for financial crime: Uses adaptive behavioral analytics to identify unusual customer and transaction behavior, helping fraud teams detect activity that static rules may miss.
Real-time transaction monitoring: Designed to monitor financial events as they happen, which makes it useful for detecting suspicious post-login activity, payment fraud, and account misuse.
Banking and regulated-market focus: Built for financial institutions that need fraud detection and financial crime prevention within controlled, compliance-heavy environments.
False-positive reduction: Publicly states that its platform has helped reduce false positive alerts by 75%, which is valuable for teams dealing with heavy alert volumes.
Enterprise risk decisioning: Its ARIC Risk Hub functions as a centralized risk decision engine for fraud and AML use cases, which helps large institutions bring multiple risk workflows into one environment.
While Featurespace is strong for anomaly detection and transaction monitoring, there are a few fit considerations to evaluate:
The platform is best suited for organizations that already have mature fraud operations and enough transaction data to support enterprise risk models.
It is also more focused on post-login and transaction-level risk, so teams looking for full-lifecycle ATO prevention across onboarding, device intelligence, identity risk, and session behavior may still need broader coverage.
Best for: Large banks and financial institutions that focus on post-login transactions.
4. Sift
Sift is a digital fraud prevention platform that helps businesses detect account takeover, payment fraud, policy abuse, and other forms of online risk. Its platform is powered by a global data network of around 1 trillion annual events across 700+ brands, which helps teams identify suspicious behavior across users, accounts, and transactions at scale.
Key strengths:
Broad digital fraud coverage: Covers account takeover, payment fraud, and first-party abuse, which makes it useful for digital businesses that want one platform for multiple fraud use cases.
Cross-account intelligence: Connects user, account, and transaction signals to help detect coordinated fraud patterns across large digital ecosystems.
Real-time risk decisioning: Evaluates risk quickly across user journeys, helping teams stop suspicious activity before it turns into financial or reputational damage.
Strong marketplace and platform fit: Works well for online marketplaces, SaaS platforms, and high-volume digital businesses where fraud often moves across accounts, payments, and policy abuse.
Machine learning and behavioral analysis: Sift’s ATO prevention uses machine learning and behavioral analysis to detect fraudulent logins and compare activity with patterns of good and bad behavior.
While Sift offers strong cross-account fraud detection, teams should evaluate where they need the most protection:
Its strength is broad digital fraud monitoring across login, account changes, transactions, and abuse patterns.
Sift’s broader fraud coverage can be useful, but teams may need careful configuration to avoid noisy rules or unnecessary reviews.
For businesses that need deeper identity verification, device-first risk detection, and lifecycle orchestration from onboarding through transactions, a more unified risk decisioning platform may be a better fit.
Best for: Marketplaces, SaaS platforms, and digital businesses that need post-login ATO monitoring.
5. Riskified
Riskified is an e-commerce-focused fraud prevention platform built around transaction risk, chargeback protection, and account security. Its Account Secure solution helps merchants detect account takeover attempts at login and checkout by comparing current sessions with past account-owner behavior and issuing allow, notify, or challenge decisions.
Key strengths:
Strong ecommerce fraud focus: Built for online merchants that need to protect checkout flows, reduce chargebacks, and approve more legitimate orders.
ATO protection tied to commerce journeys: Its Account Secure product helps detect malicious login attempts, credential-stuffing bots, and suspicious account activity in retail and ecommerce environments.
Transaction history as a risk signal: Uses transaction history from the merchant and its wider merchant network to improve account-risk decisions.
Chargeback protection: Riskified’s Chargeback Guarantee helps merchants reduce fraud-related chargeback exposure, which is especially valuable for high-volume ecommerce brands.
While Riskified is strong for e-commerce fraud and chargeback protection, there are a few scope and fit considerations to evaluate:
The platform is primarily commerce-oriented, so its strongest fit is checkout, transaction risk, and account protection tied to purchase journeys.
Teams that need ATO prevention before checkout, such as onboarding fraud, identity takeover, or session hijacking detection, may need broader lifecycle coverage.
Riskified’s value is closely tied to e-commerce transaction volume, which may make it less relevant for fintech, digital banking, or non-commerce platforms.
Best for: E-commerce brands and online retailers that need ATO tied to payments and chargeback management.
6. Kount
Kount, an Equifax company, provides fraud prevention capabilities across account protection, new account fraud, payments, and digital trust. Its account protection solution helps prevent login fraud, fake account creation, and takeover fraud using device, email, phone, address, AI, machine learning, reporting, and analytics signals.
Key strengths:
Device intelligence foundation: Kount uses device and identity signals to identify suspicious activity, repeat offenders, and risky account behavior across digital journeys.
Account protection coverage: Kount 360 Account Protection supports login protection, new account fraud prevention, and account takeover prevention.
Customizable fraud policies: Kount allows merchants to manage, customize, and adjust account takeover policies inside the platform without heavy development requirements.
Real-time reporting: Kount Control supports reporting on failed login attempts, risky IP addresses, compromised accounts, and other inbound anomalies.
Retail and e-commerce alignment: Kount is especially relevant for businesses that need to detect fake accounts, promo abuse, card testing, and repeat fraud behavior across digital commerce flows.
While Kount offers practical device-led fraud prevention, there are a few signal and coverage considerations to evaluate:
Behavioral biometrics are not its core signal, so teams needing deep session-level behavior analysis may need additional coverage.
Businesses with complex identity-risk needs may need to assess whether Kount provides enough context across linked accounts, mule networks, and coordinated fraud rings.
For teams looking for a single system across onboarding, login, session behavior, and transactions, Kount may need to work alongside other fraud and identity tools
Best for: E-commerce and retail businesses that focus on login and post-login fraud detection.
How Does Bureau ID Help With ATO?
Most tools tend to focus on a single layer of the fraud lifecycle, which often leaves gaps that attackers exploit.
In fact, Bureau ID's 2026 India Fraud Report found that 48% of Indian enterprises identify mule networks as the most difficult fraud threat to detect and control, ahead of phishing, synthetic identities, account takeover, and social engineering.
That finding matters for ATO because compromised accounts often become part of wider fraud networks, which are difficult to detect when each account is reviewed in isolation.
Bureau ID takes a more connected approach by bringing together device, identity, behavioral, and transaction signals into a single system, enabling continuous risk evaluation across the entire user journey.
Step 1: Device Intelligence
Bureau ID starts by identifying the device at the very first interaction. Instead of waiting for login attempts, the platform evaluates signals such as device configuration, spoofing attempts, emulator usage, and SIM swap indicators early in the journey.
This early visibility helps flag suspicious activity before credentials even come into play, which reduces reliance on passwords as the primary line of defense.
Step 2: Identity Verification
Once the device is assessed, the platform connects the user to a broader identity context. Bureau ID cross-references signals against its identity graph, which helps surface shared devices, linked accounts, and unusual identity patterns.
This approach shifts detection from looking at individual users in isolation to understanding how they connect within larger fraud networks.
Step 3: Behavioral Biometrics
As the session progresses, behavioral biometrics add another layer of insight. Bureau ID continuously monitors how users interact with the platform, including navigation flow, interaction speed, and usage patterns.
These signals help distinguish genuine users from bots, scripted attacks, or remote access tools that often mimic normal activity but fail to replicate natural behavior.
Step 4: Real-Time Risk Decisioning
Security teams describe seeing more account takeovers tied to token theft and phishing kits that make MFA bypass easier. That practitioner-level concern supports why ATO prevention cannot stop at login or OTP checks; risk needs to be evaluated across devices, sessions, and account activity.
All of these signals come together in a unified decisioning layer. Bureau ID evaluates risk in real time and assigns a score based on the combined context of device, identity, and behavior. Instead of applying blanket verification methods, the system triggers adaptive authentication only when the risk level warrants intervention.
This ensures that genuine users move smoothly while suspicious activity faces appropriate friction.
Step 5: Continuous Monitoring and Feedback
Detection does not stop after login. Bureau ID continues to monitor activity across sessions, transactions, and account changes. These signals feed back into the system, which allows risk models to evolve and improve over time.
This continuous loop helps reduce false positives while strengthening detection accuracy as new fraud patterns emerge.
When these layers work together, account takeover detection starts to understand behavior across the full lifecycle, allowing businesses to move from reactive fraud handling to proactive prevention, without compromising the user experience.
Implementation Framework: How to Deploy ATO Prevention Without Breaking UX?
Most teams run into the same trade-off sooner or later. The moment security gets stricter, user experience starts to suffer. More friction leads to higher drop-offs, abandoned sessions, and frustrated users. The challenge is designing a system where both security and experience work together.
This balance matters because fragmented controls make fraud harder to catch early. Bureau ID’s UK and EU Fraud Report found that 67% of organizations say siloed systems prevent early signal correlation, while 50% faced device spoofing and emulator-based activity. That makes a strong case for ATO prevention that connects identity, device, behavior, and transaction signals before adding more friction.
A practical way to approach this is to break the problem down across the user journey instead of treating ATO as a single checkpoint.
Start by mapping high-risk points across the journey: Not every stage carries the same level of risk, and treating them equally often leads to unnecessary friction. Focus on areas where fraud typically shows up:
Onboarding flows where fake or synthetic identities enter the system
Login attempts, especially from new or unrecognized devices
Password resets and account recovery flows, which attackers often exploit
Transactions or account changes that involve financial or sensitive actions
Once these touchpoints are clear, the next step is to understand what signals you actually have in place.
Audit your signal coverage before adding new controls: Many systems rely heavily on credentials or OTPs (one-time passwords), which creates blind spots once those signals are compromised. A more complete setup includes:
Device intelligence to identify spoofing, emulators, and repeat offenders
Behavioral analytics to track how users interact during sessions
Identity signals that connect users across accounts and environments
Gaps in any of these areas often explain why fraud bypasses existing defenses.
Define risk thresholds based on context, not assumptions: A login from a trusted device should not trigger the same response as one from a new location or unfamiliar device. Risk needs to be evaluated per action:
Low-risk activity should move forward without interruption
Medium-risk activity may require light verification
High-risk activity should trigger stronger step-up checks
This layered approach prevents over-securing routine actions while still catching suspicious behavior.
Apply adaptive authentication with precision: Instead of enforcing MFA across every interaction, apply it only when risk signals justify it. This reduces unnecessary friction and keeps genuine users moving through the flow without disruption. The goal is to challenge only when something feels off, not by default.
Continuously monitor and refine detection models: ATO prevention does not end at login. Fraud patterns evolve quickly, and detection systems need to adapt just as fast. Continuous monitoring helps teams:
Track session behavior and post-login activity
Identify false positives and refine thresholds
Adjust rules without long development cycles, especially with no-code workflows
Over time, this feedback loop improves both detection accuracy and user experience.
The core idea behind this framework is simple. Precision matters more than restriction, and the systems that succeed are the ones that apply friction selectively rather than universally. When detection aligns with real user behavior, security changes from a barrier to an invisible layer that works exactly when it should.
Related Read: The Key Reasons Fraud Continues to Outpace Defenses in the UK and EU
Build a Defense That Covers the Full Journey
Basic ATO defenses solve one part of the journey, but attackers do not operate that simply. They move across onboarding, login, sessions, account changes, and payments until they find the weakest point.
The next step is to evaluate whether your current setup connects device intelligence, behavioral signals, identity context, and real-time risk decisioning in one place. If those signals sit across separate tools, your team may still miss the patterns that reveal coordinated fraud.
When you work with Bureau ID, the team can help you assess where ATO risk appears in your user journey, which signals you already capture, and where fraud may be slipping through. From there, they can help you build a risk decisioning flow that applies friction only when needed, while letting genuine users move forward smoothly.
If you are ready to move from isolated fraud checks to full-journey ATO prevention, schedule a demo with Bureau ID and see how its unified risk decisioning platform can support your account takeover prevention strategy.
FAQs
1. What is account takeover prevention software?
Account takeover prevention software protects user accounts from unauthorized access. The software detects suspicious logins, stolen credentials, and bot-driven attacks in real time. The system analyzes device signals, user behavior, and session activity to identify anomalies. The goal is to stop fraud before attackers gain control of accounts.
2. What are the best account takeover prevention software tools?
Top account takeover prevention software tools include Bureau ID, BioCatch, Featurespace, Sift, Riskified, and Kount. These platforms focus on different strengths such as behavioral biometrics, fraud analytics, device intelligence, and real-time risk decisioning. Businesses compare these tools based on detection accuracy, integration, scalability, and ability to reduce fraud without increasing login friction.
3. Why is Bureau ID a strong option for account takeover prevention?
Bureau ID offers a multi-layered approach to account takeover prevention. The platform combines device intelligence, identity verification, behavioral biometrics, and real-time risk decisioning. This approach helps detect suspicious activity early and block unauthorized access. Continuous monitoring improves detection over time. The system focuses on reducing fraud while maintaining a smooth user experience.
4. How does account takeover prevention software work?
Account takeover prevention software analyzes login activity, device signals, and user behavior. The system assigns risk scores based on anomalies such as unusual locations or rapid login attempts. High-risk sessions trigger adaptive authentication. Continuous monitoring tracks session activity to detect hijacking or unauthorized changes.
5. Can account takeover prevention software stop bot attacks and credential stuffing?
Account takeover prevention software detects and blocks automated login attempts. The system identifies patterns such as rapid login requests, reused credentials, and abnormal traffic. Bot detection and credential intelligence help prevent large-scale credential-stuffing attacks before accounts are compromised.
6. How does account takeover prevention software protect accounts without adding login friction?
Account takeover prevention software uses adaptive authentication and risk-based controls. Low-risk users access accounts without interruption. High-risk activity triggers additional verification. Behavioral analytics and device recognition help maintain security while minimizing unnecessary login challenges.
TABLE OF CONTENTS
See More
Recommended Blogs
Landing Page.
Simple, bold.
Sign Up
Download

Products
Solutions
Resources
© 2026 Bureau . All rights reserved.
Solutions
Industries
Resources
Company
Solutions
Industries
Resources
Company
© 2026 Bureau . All rights reserved.
Follow Us
Leave behind fragmented tools. Stop fraud rings, cut false declines, and deliver secure digital journeys at scale
Our Presence











Leave behind fragmented tools. Stop fraud rings, cut false declines, and deliver secure digital journeys at scale
Our Presence











© 2026 Bureau . All rights reserved.




